A consortium of which the company is a part has made working versions of ultradense seven-nanometer chips, capable of holding much more information than existing chips.
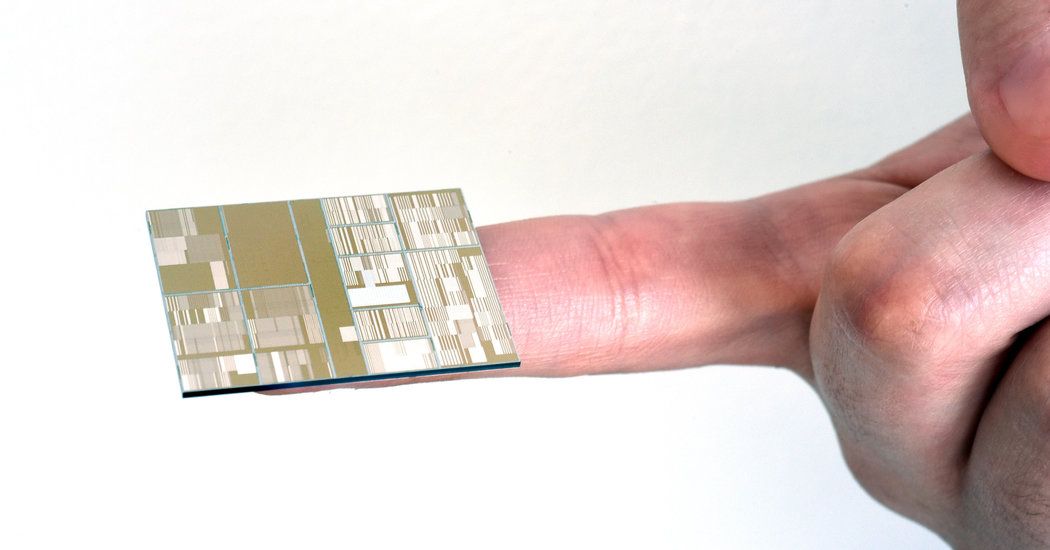
A consortium of which the company is a part has made working versions of ultradense seven-nanometer chips, capable of holding much more information than existing chips.

IBM’s newest computer chips contain seven-nanometer transistors. As points of comparison, a strand of DNA is about 2.5 nanometers in diameter and a red blood cell is roughly 7,500 nanometers in diameter.
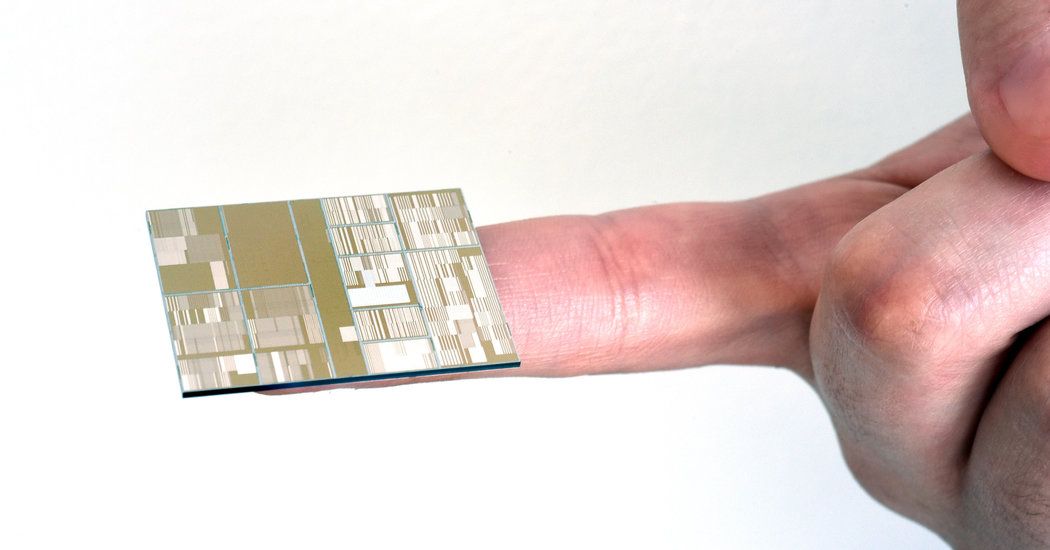
Digital Reasoning has trained a record-breaking artificial intelligence neural network that is 14 times larger than Google’s previous record.

Last year, Google began experimenting with hardware-based schemes for user-authentication, while Apple added two factor authentication to iCloud and Apple ID users. They began sending a verification code to users via a mobile number registered in advance.
Security pundits know that two factor authentication is more secure than simple passwords. As a refresher, “Factors” are typically described like this:
The Google project may be just another method of factor #2. In fact, because it is small (easily misplaced or stolen), it simplifies but does not improve on security. I suggest a radical and reliable method of authentication. It’s not new and it’s not my idea…
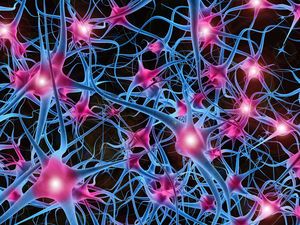
Back in 1999, Hugh Davies (no relation to Ellery) was awarded a patent on a novel form of access and authentication. It capitalizes on the human ability to quickly pick a familiar face out of a crowd. Just as with passwords, it uses something that you know to log in, purchase, or access a secure service. But unlike passwords, the “combination” changes with every use, and yet the user needn’t learn anything new.
Hoping to commercialize the technique, Davies joined another Brit, Paul Barrett, and formed Passfaces (originally, Real User Corporation). Incidentally, it is quite difficult to research Passfaces and its history. Web searches for “face recognition”, “access”, “authentication” and “patent” yield results for a more recent development in which a smart phone recognizes the face of authorized users, rather than users recognizing familiar faces. (Google, Samsung and Apple are all beginning to use face recognition on mobile devices). In fact, the Passfaces method is quicker, uses less resources and is far more reliable.
I have long been disappointed and surprised that the technique has never caught on. It is a terrific method with few drawbacks. Used alone, it is better than other methods of 1 or 2 factor authentication. Add a second factor and it is remarkably secure and robust.
How it Works:
 When accessing or authenticating (for example, logging into a corporate VPN or completing a credit card purchase), you are presented with a tiled screen of individual faces. I prefer a big 15×5 grid = 75 images, but Passfaces uses sequential screens of just 9 faces arranged like the number pad on an ATM.
When accessing or authenticating (for example, logging into a corporate VPN or completing a credit card purchase), you are presented with a tiled screen of individual faces. I prefer a big 15×5 grid = 75 images, but Passfaces uses sequential screens of just 9 faces arranged like the number pad on an ATM.
Just click on a few familiar faces. That’s all! Oddly, Passfaces discourages the use of known faces. Their research, with which I respectfully disagree, suggests that users should train themselves to recognize a few faces from the company’s stock library. In my preferred embodiment, users upload a dozen photos of people they know at a glance—preferably, people that they knew in the past: A 3rd grade music teacher, a childhood friend who moved away, the face on an oil painting that hung in the basement until Dad tossed it in the fireplace. Now, add the boss who fired you from your first job, the prom queen who dumped you for a football jock, and that very odd doorman who stood in front of a hotel in your neighborhood for 20 years. Photos of various quality and resolution, but all scaled to fit the grid. Some are black & white, perhaps scanned from an old yearbook.
Using my preferred example of 75 faces, suppose that 5 or 6 of the images are from your personal shoe box of old photos. The rest are randomly inserted from all over the internet. How long would take you to click on 3 of the 5 or 6 familiar faces in front of you? (Remember: They are old acquaintances. Even a spouse would have difficulty picking out 3 faces from your early life—as they looked back then). Surprise! You will click them instantly, especially on a touch screen. You won’t need even a second to study the collage. They jump off the screen because your brain perceives a familiar face very differently and faster than anything else.
Of course, the photo array is mixed in different ways for each authentication and it incorporates different friends from your original upload. In fact, if a user sees the same faces in the next few transactions, it is a red flag. Someone has spied on the process, perhaps with a local camera or screen logger. In legitimate use, the same faces are not recycled for many days and are never shown together on the same screen.
Facebook uses a variant of this technique when their servers sense your attempt to login from new equipment or from another part of the country. They show you individuals that you have friended, but that were uploaded and tagged by other users. If you cannot identify a few of your own friends, especially the ones with which you have frequent social contact, than it’s likely that your login attempt deserves more scrutiny.
I don’t know why Passfaces or something like it has failed to catch fire. Perhaps the inventor refuses to license the method at reasonable cost or perhaps he cannot find a visionary VC or angel consortium to more aggressively promote it. If I had invented and patented facial-array authentication, I would attempt to market the patent for a short time focusing on very large network companies like Microsoft, Google, Cisco or Akamai. If I could not license or sell the patent quickly, I would hesitate to go it alone. (I have tried that route too many times). Instead, I would place it in the public domain and profit by being the first, and most skilled practitioner at deployment. I would train and certify others and consult to organizations that use or commercialize the technology.
 I used this approach in promoting my own patent which describes an economic barrier to spam (after failing to exploit the invention with my own company). Later, I started with this approach in my research on Blind Signaling and Response and on Reverse Distributed Data Clouds. I recognized that rapid adoption of transformative technology like facial grid authentication, can be thwarted by defensive IP practice.
I used this approach in promoting my own patent which describes an economic barrier to spam (after failing to exploit the invention with my own company). Later, I started with this approach in my research on Blind Signaling and Response and on Reverse Distributed Data Clouds. I recognized that rapid adoption of transformative technology like facial grid authentication, can be thwarted by defensive IP practice.
« Branching somewhat off topic, a developmental biologist at Imperial College in London, has published a proof that Saira Mohan has the world’s most beautiful face, irrespective of the observer’s race. That’s Saira at left. Her mother is French/Irish and her father is Hindoo.
__________
Philip Raymond is Co-Chair of The Cryptocurrency Standards Association [crypsa.org] and
chief editor at AWildDuck.com. He consults to cloud storage vendors in areas of security, pri–
vacy & network architecture, but has no ties to Passfaces or the authentication community.

Say hello to the future of communication.…. FTL communication, possibly! (not to mention quantum computing, etc etc etc)

“It would have been crazy to say just a few years ago. But today, Google produces better-designed software than any other tech behemoth. If you don’t believe that, then set down your Apple-flavored Kool-Aid. Take a cleansing breath, open your mind, and compare Android and iOS.”
“They begin by pointing out the extraordinary successes of human computation. One of the most notable is the Fold.it project in which participants are asked to fold virtual proteins in the most efficient way possible. The goal is to solve one of the most important outstanding problems in molecular biology: how proteins fold so rapidly and efficiently. The project has had some impressive successes. Soon after it began, it discovered the tertiary structure of a regulatory protein for the pros-simian immunodeficiency virus, a problem the research community had puzzled over for decades and one that that could lead to new ways of tackling the AIDS virus.” Read more
[youtube_sc url=“https://www.youtube.com/watch?v=m5WodTppevo” loop=“1”]
” “Following these rules, we’ve demonstrated that we can make all the universal logic gates used in electronics, simply by changing the layout of the bars on the chip,” said Katsikis. “The actual design space in our platform is incredibly rich. Give us any Boolean logic circuit in the world, and we can build it with these little magnetic droplets moving around.”
The current paper describes the fundamental operating regime of the system and demonstrates building blocks for synchronous logic gates, feedback and cascadability – hallmarks of scalable computation. A simple-state machine including 1-bit memory storage (known as “flip-flop”) is also demonstrated using the above basic building blocks. ”
Small gadgets such as smart watches can be frustrating to use because their tiny buttons and touch screens are tricky to operate. Google has two possible solutions for the fat finger problem: control your gadgets by subtly rubbing your finger and thumb together, or by swiping a grid of conductive yarn woven into your clothing.
The first of those two ideas works thanks to a tiny radar sensor that could be integrated into, say, a smart watch and can detect fine motions of your hands from a distance and even through clothing. Levi Strauss announced today that it is working with Google to integrate fabric touch panels into its clothing designs. The new projects were announced at Google’s annual developer conference in San Francisco Friday by Ivan Poupyrev, a technical program lead in Google’s Advanced Technology and Projects research group.

“Canada’s domestic digital divide, with the North as its epicenter, has been a point of growing concern over the last several years. Much of the internet in the northernmost regions of the country is still beamed down by satellites, but a plan to link Europe and Asia with fiber optic cable via Nunavut is currently being negotiated by a Toronto-based company called Arctic Fibre.”