A mathematical equation has proven that controlling one of the two major changes in a cell—decay or cancerous growth—enhances the other, causing inevitable death.


A mathematical equation has proven that controlling one of the two major changes in a cell—decay or cancerous growth—enhances the other, causing inevitable death.
In their book “Era of Exponential Encryption — Beyond Cryptographic Routing” the authors provide a vision that can demonstrate an increasing multiplication of options for encryption and decryption processes: Similar to a grain of rice that doubles exponentially in every field of a chessboard, more and more newer concepts and programming in the area of cryptography increase these manifolds: both, encryption and decryption, require more session-related and multiple keys, so that numerous options even exist for configuring hybrid encryption: with different keys and algorithms, symmetric and asymmetrical methods, or even modern multiple encryption, with that ciphertext is converted again and again to ciphertext. It will be analyzed how a handful of newer applications like e.g. Spot-On and GoldBug E-Mail Client & Crypto Chat Messenger and other open source software programming implement these encryption mechanisms. Renewing a key several times — within the dedicated session with “cryptographic calling” — has forwarded the term of “perfect forward secrecy” to “instant perfect forward secrecy” (IPFS). But even more: if in advance a bunch of keys is sent, a decoding of a message has to consider not only one present session key, but over dozens of keys are sent — prior before the message arrives. The new paradigm of IPFS has already turned into the newer concept of these Fiasco Keys are keys, which provide over a dozen possible ephemeral keys within one session and define Fiasco Forwarding, the approach which complements and follows IPFS. And further: by adding routing- and graph-theory to the encryption process, which is a constant part of the so called Echo Protocol, an encrypted packet might take different graphs and routes within the network. This shifts the current status to a new age: The Era of Exponential Encryption, so the vision and description of the authors. If routing does not require destination information but is replaced by cryptographic in.

RSA Encryption is an essential safeguard for our online communications. It was also destined to fail even before the Internet made RSA necessary, thanks the work of Peter Shor, whose algorithm in 1994 proved quantum computers could actually be used to solve problems classical computers could not.


In recent years, forensics scientists, statisticians, and engineers have been working to put crime scene forensics on a stronger footing, with some classic techniques falling out of favor.
[Photos: OpenClipart-Vectors/Pixabay; Hunter Harritt/Unsplash; blickpixel/Pixabay].
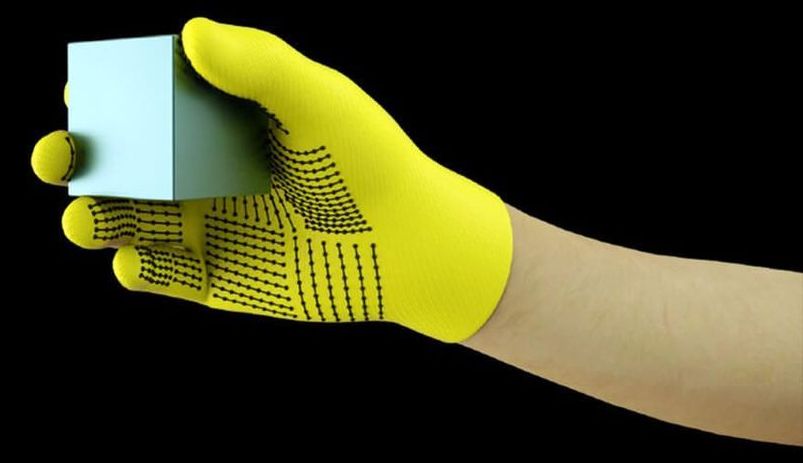
Machines are mastering vision and language, but one sense they’re lagging behind on is touch. Now researchers have created a sensor-laden glove for just $10 and recorded the most comprehensive tactile dataset to date, which can be used to train machine learning algorithms to feel the world around them.
Dexterity would be an incredibly useful skill for robots to master, opening up new applications everywhere from hospitals to our homes. And they’ve been coming along in leaps and strides in their ability to manipulate objects, OpenAI’s cube juggling robotic hand being a particularly impressive example.
So far, though, they’ve had one hand tied behind their backs. Most approaches have relied on using either visual data or demonstrations to show machines how they should grasp objects. But if you look at how humans learn to manipulate objects, you realize that’s just one part of the puzzle.
Also, loosely following technology that could be used to build a real working time machine. Anyone with an interest in time travel is welcome to participate.
But, I have been watching tech news for what could be used to build a time machine. I think we are pretty close. You’d still need a few physics guys with 150+ IQ’s to work on the equations, a guy with a 200+ IQ to figure out how to put the whole thing together, and a guy with billions of dollars to fund it. But most of this stuff is for sale to the public, (short list):
1. quantum computer; to run the calculations.

This post was prompted by a colleague sharing with me this recent study: www.ncbi.nlm.nih.gov/pmc/articles/PMC6389801/
The authors found that out of 516 studies evaluating the performance of ML algorithms for the diagnostic analysis of medical images, only 31 had externally validated their algorithms.
This should concern us all.

Abstract: In standard nonrelativistic quantum mechanics the expectation of the energy is a conserved quantity. It is possible to extend the dynamical law associated with the evolution of a quantum state consistently to include a nonlinear stochastic component, while respecting the conservation law. According to the dynamics thus obtained, referred to as the energy-based stochastic Schrodinger equation, an arbitrary initial state collapses spontaneously to one of the energy eigenstates, thus describing the phenomenon of quantum state reduction. In this article, two such models are investigated: one that achieves state reduction in infinite time, and the other in finite time. The properties of the associated energy expectation process and the energy variance process are worked out in detail. By use of a novel application of a nonlinear filtering method, closed-form solutions—algebraic in character and involving no integration—are obtained for both these models. In each case, the solution is expressed in terms of a random variable representing the terminal energy of the system, and an independent noise process. With these solutions at hand it is possible to simulate explicitly the dynamics of the quantum states of complicated physical systems.
From: Dorje C. Brody [view email]
[v1] Mon, 29 Aug 2005 13:22:36 UTC (43 KB)