Technology like sensors built into infrastructure and emergency alerts has possible benefits, but in a new study dozens of experts weigh in on where some of the more significant pitfalls may lie.



Partners.
Banco Santander.
IBM
International Criminal Police Organization (INTERPOL)… See More
Cyberspace by nature has no borders, which allows criminals to launch their attacks from anywhere in the world, at any time. As legal parameters are unable to keep up with the pace of technological proliferation, the absence of international laws capable of restricting the actions of attackers regardless of their geolocation gives these criminals a sense of absolute impunity. To counter this effectively, there is an urgent need to start learning the basics of working together.
What is Cyber Polygon?
Cyber Polygon is a unique cybersecurity event that combines the world’s largest technical training for corporate teams and an online conference featuring senior officials from international organisations and leading corporations.

Hungarian mathematician László Lovász and Israeli computer scientist Avi Wigderson will share the prize, worth 7.5 million Norwegian kroner (US$886000), “for their foundational contributions to theoretical computer science and discrete mathematics, and their leading role in shaping them into central fields of modern mathematics”, the Norwegian Academy of Science and Letters announced on 17 March.
The work of winners László Lovász and Avi Wigderson underpins applications from Internet security to the study of networks.

But the site’s cybersecurity measures appear to be lacking.
Several other Nifty Gateway users reported that their accounts had been hacked. “My entire account was just hacked and the person who got in wasn’t even booted after changing my password?!” one user wrote in a tweet.
According to a Nifty spokesperson who spoke to Motherboard, the company was aware of the fraudulent activity. The company claims the affected users didn’t have two-factor authentication turned on and that “access was obtained via valid account credentials.”

Cybersecurity researchers have unwrapped an “interesting email campaign” undertaken by a threat actor that has taken to distributing a new malware written in Nim programming language.
Dubbed “NimzaLoader” by Proofpoint researchers, the development marks one of the rare instances of Nim malware discovered in the threat landscape.
“Malware developers may choose to use a rare programming language to avoid detection, as reverse engineers may not be familiar with Nim’s implementation, or focused on developing detection for it, and therefore tools and sandboxes may struggle to analyze samples of it,” the researchers said.

It didn’t take long. Intelligence agencies and cybersecurity researchers had been warning that unpatched Exchange Servers could open the pathway for ransomware infections in the wake of swift escalation of the attacks since last week.
Now it appears that threat actors have caught up.
According to the latest reports, cybercriminals are leveraging the heavily exploited ProxyLogon Exchange Server flaws to install a new strain of ransomware called “DearCry.”

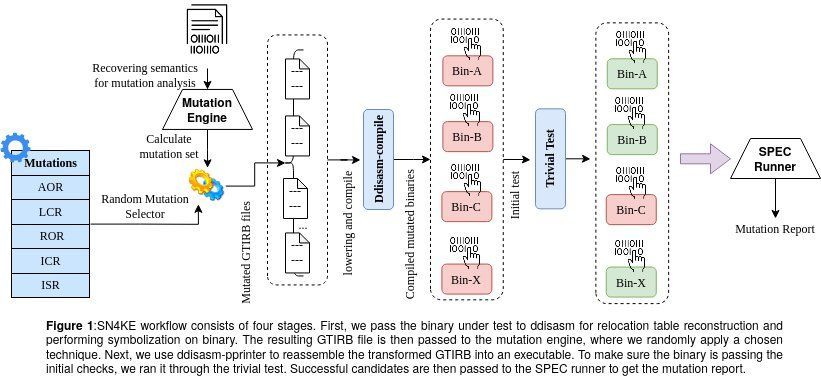
When developers deliver software to their clients, they often also provide what is known as a ‘test suite.’ A test suite is a tool that allows users to test software, unveil any bugs it might have and give developers a chance to fix these bugs or other potential issues.
In addition to evaluating software, therefore, developers also need to ascertain the efficacy of a test suite in identifying bugs and errors. One way to run test suite evaluations is via mutation testing, a technique that generates several ‘mutants’ of a program by slightly modifying its original code. While mutation testing tools have proved to be incredibly helpful, most of them cannot be applied to software that is only available in binary code (a way of representing texts or instructions for computers using two symbols, generally ‘0’ and ‘1’).
Researchers at Arizona State University, Worcester Polytechnic Institute and the University of Minnesota have recently developed SN4KE, a framework that can be used to carry out mutation analyses at a binary level. This framework, presented at the Binary Analysis Research (BAR) NDSS symposium ‘21 in February, is a new tool to efficiently test suites for software based on binary codes.

A new type of supply chain attack unveiled last month is targeting more and more companies, with new rounds this week taking aim at Microsoft, Amazon, Slack, Lyft, Zillow, and an unknown number of others. In weeks past, Apple, Microsoft, Tesla, and 32 other companies were targeted by a similar attack that allowed a security researcher to execute unauthorized code inside their networks.
The latest attack against Microsoft was also carried out as a proof-of-concept by a researcher. Attacks targeting Amazon, Slack, Lyft, and Zillow, by contrast, were malicious, but it’s not clear if they succeeded in executing the malware inside their networks. The npm and PyPi open source code repositories, meanwhile, have been flooded with more than 5000 proof-of-concept packages, according to Sonatype, a firm that helps customers secure the applications they develop.
“Given the daily volume of suspicious npm packages being picked up by Sonatype’s automated malware detection systems, we only expect this trend to increase, with adversaries abusing dependency confusion to conduct even more sinister activities,” Sonatype researcher Ax Sharma wrote earlier this week.