I must admit; I got a little laughter from reading the beginning of this article. However, there is a potential longer term concern around jobs and an even larger concern around data (including IP) when it comes to AI. So, I truly hope folks are strategically planning, designing, and implementing appropriate safeguards around their AI architecture and systems; especially if we look at hacking, etc.
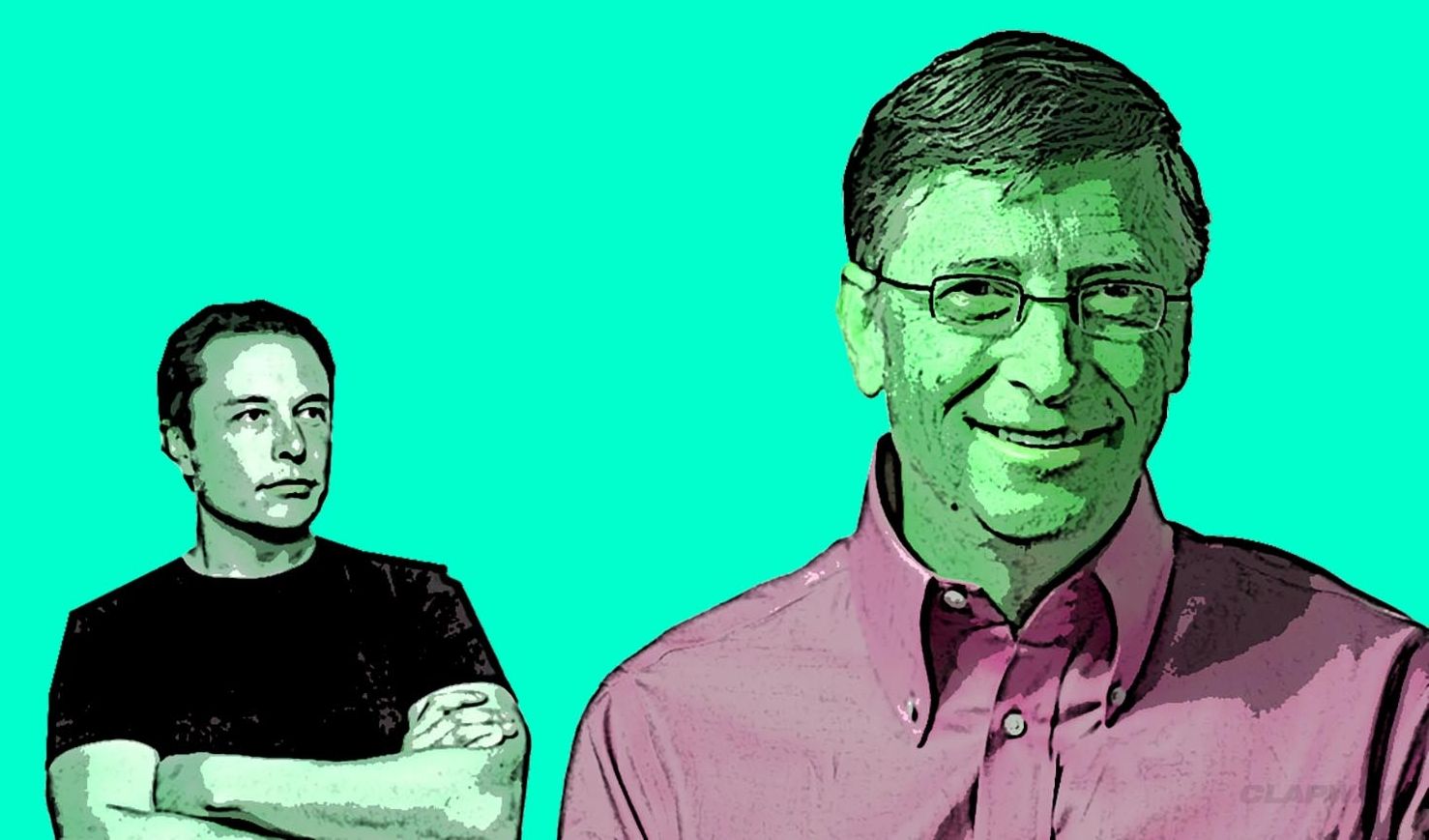
Bill Gates, Elon Musk and Stephen Hawking have all done their part in warning the world of the true power of artificial intelligence. All three men were actually awarded the 2015 Luddite Award, which is given by the Information Technology & Innovation Foundation.
Because of their honest assessment on the power of new technology, these three men have been called alarmists who spread horror. There were 10 total nominees to the prices, and all three received them after getting more 3,680 votes.
Luddite is a word from 19th century England, and it is used to describe someone who is opposed to advances in technology. This is hardly an appropriate denomination for any of these men. Bill Gates is almost single-handedly responsible for putting PC computers in homes, Elon Musk has made a revolution with electric vehicles. Volumes can be written on the impact Stephen Hawking has had on the world.
Read more