A clever attack by French researchers turns your headphone cable into an antenna to send surreptitious voice commands.


A clever attack by French researchers turns your headphone cable into an antenna to send surreptitious voice commands.
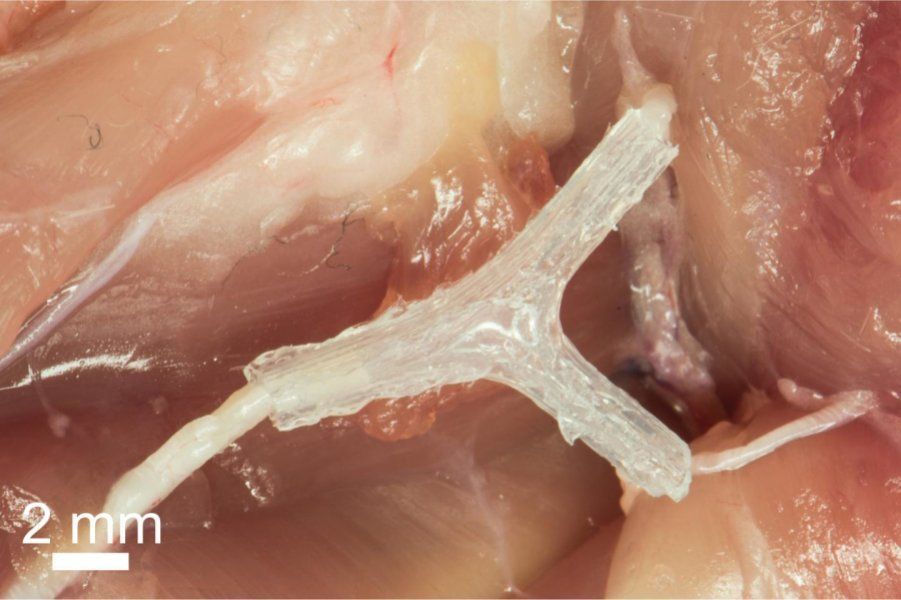
Having significantly damaged nerve tissue is bad for a lot of reasons because it doesn’t regenerate easily and it can lead to various serious medical conditions including paralysis. But many scientists are already studying ways of fixing this issue, and a team of researchers from the University of Minnesota, Virginia Tech, University of Maryland, Princeton University, and Johns Hopkins University has figured out how to use 3D printing for nerve growth.
DON’T MISS: 85 legitimate iPhone apps that were infected with malware in the big App Store hack
The technology they’ve developer has allowed them to regrow nerve tissue in lab rats and restore normal walking ability 10 to 12 weeks after the 3D printed guide was implanted.

From helicopters to medical devices and power stations, mathematical proof that software at the heart of an operating system is secure could keep hackers out.
China is set to complete the installation of the world’s longest quantum communication network stretching 2,000km (1,240miles) from Beijing to Shanghai by 2016, say scientists leading the project. Quantum communications technology is considered to be “unhackable” and allows data to be transferred at the speed of light.
By 2030, the Chinese network would be extended worldwide, the South China Morning Post reported. It would make the country the first major power to publish a detailed schedule to put the technology into extensive, large-scale use.
The development of quantum communications technology has accelerated in the last five years. The technology works by two people sharing a message which is encrypted by a secret key made up of quantum particles, such as polarized photons. If a third person tries to intercept the photons by copying the secret key as it travels through the network, then the eavesdropper will be revealed by virtue of the laws of quantum mechanics – which dictate that the act of interfering with the network affects the behaviour of the key in an unpredictable manner.

In the first documented attack of its kind, the Internet of Things has been used as part of an attack that sent out over 750,000 spam emails. .

How about security hacking as a form of Turing’s Test?
“Next year’s Cyber Grand Challenge event will pit humans against machines in a grand hacking war”
Next year’s Cyber Grand Challenge event will pit humans against machines in a grand hacking war. DEF CON’s war gamers like their chances.

Fiat-Chrysler said today it was launching a voluntary recall of 1.4 million vehicles after a Jeep Cherokee was hacked remotely for the first time.
Every 15 seconds, a computer, network, or mobile device is hacked by cyber-terrorists. To combat this problem, Syntek Industries has manufactured data couriers designed from advanced machine robotics. These couriers are known as SYNCS. Syncs are programmed to securely deliver data packages without interruption.

By Peter Diamandis — SingularityHub
This blog is about the downside of exponential technology: digital crime.
Normally, I choose to focus on the immensely positive impact technology has on humanity – the Abundance mindset.
Sarah Buhr — Tech Crunch
Edward Snowden says in a new interview with NOVA Next that the U.S. government wrongly promotes cyber offense strategies at the expense of weakening the system and leaving it open to cyber attacks from the black market.
“We’re creating a class of Internet security researchers who research vulnerabilities, but then instead of disclosing them to the device manufacturers to get them fixed and to make us more secure, they sell them to secret agencies,” Snowden says. “They sell them on the black market to criminal groups to be able to exploit these to attack targets. And that leaves us much less secure, not just on an individual level, but on a broad social level; on a broad economic level. And beyond that, it creates a new black market for computer weapons, basically digital weapons.”