The idea of a tritium power cell is pretty straightforward: stick enough of the tiny glowing tubes to a photovoltaic panel and your DIY “nuclear battery” will generate energy for the next decade or so. Only problem is that the power produced, measured in a few microwatts, isn’t enough to do much with. But as [Ian Charnas] demonstrates in his latest video, you can eke some real-world use out of such a cell by storing up its power over a long enough period.
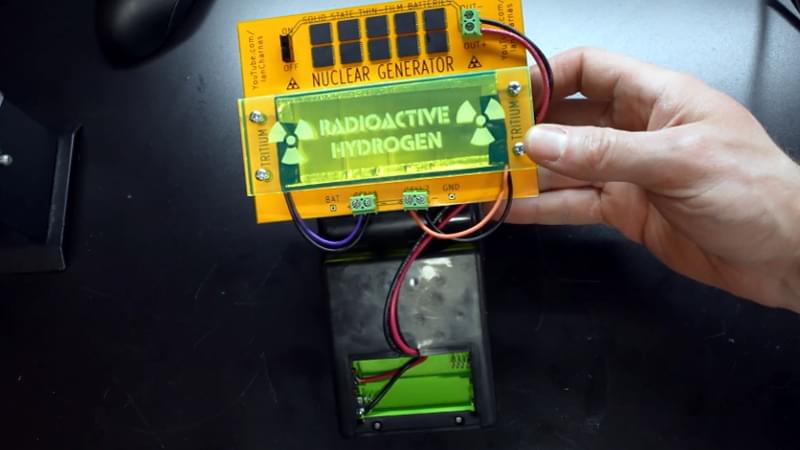
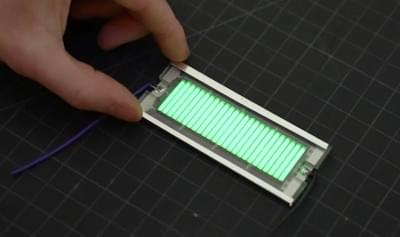
As with previous projects we’ve seen, [Ian] builds his cell by sandwiching an array of keychain-sized tritium tubes between two solar panels. Isolated from any outside light, power produced by the panels is the result of the weak green glow given off by the tube’s phosphorus coating as it gets bombarded with electrons. The panels are then used to charge a bank of thin-film solid state batteries, which are notable for their exceptionally low self-discharge rate.
Some quick math told [Ian] that a week of charging should build up enough of a charge to power a knock-off handheld Tetris game for about 10 minutes. Unfortunately, after waiting the prescribed amount of time, he got only a few seconds of runtime out of his hacked together power source.