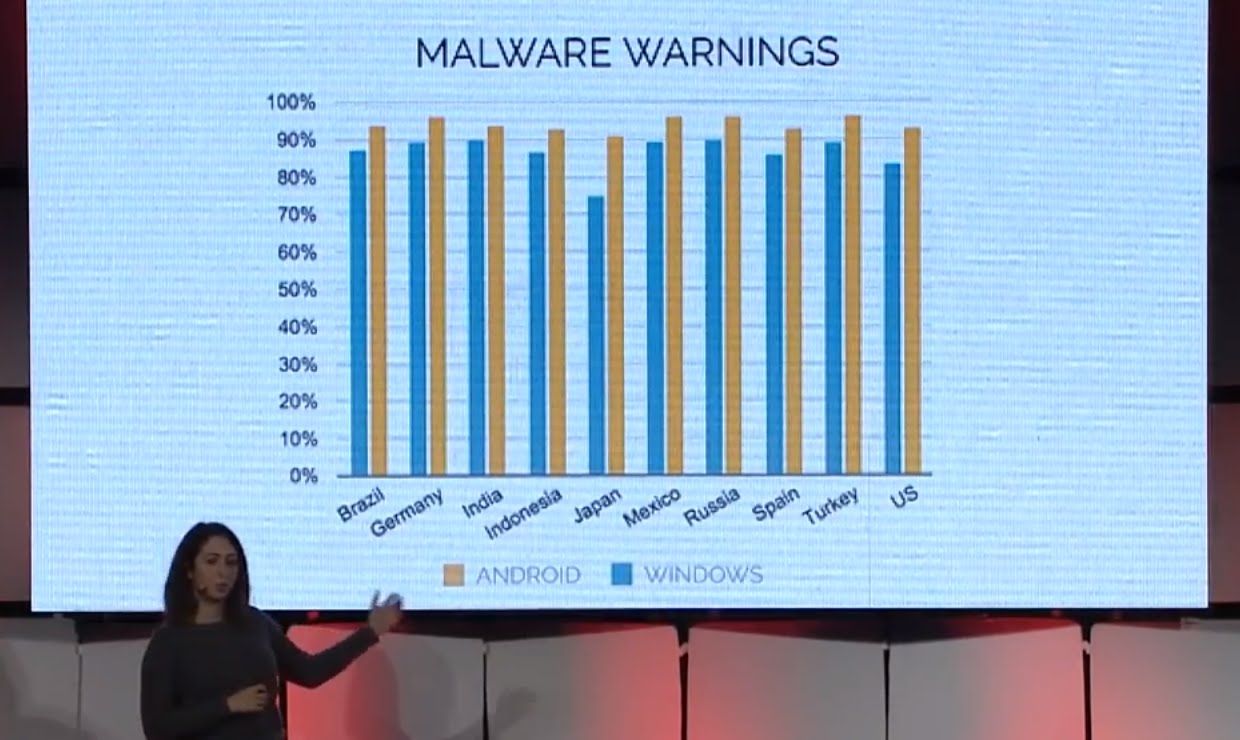
Tough to be a doctor these days — Could be bad news for Providers with limited or no Cyber Risk Coverage.
Providers are focusing on cybersecurity with increased urgency. Cyberattacks on health-care organizations reached an all-time high in 2015 and aren’t expected to slow down in 2016, Harry Greenspun, director for Deloitte’s Center for Health Solutions, told Bloomberg BNA. One element of a comprehensive strategy to address data security is customized cyber risk insurance. Recent case law supports standing for class action litigants alleging future injuries, which may not be covered by some policy forms. We urge providers to review their cyber risk coverage with the increasing risks and this new case law in mind.
Specifically, it is critical that cyber risk insurance is designed to both: adequately mitigate future harm to those whose private information is compromised as a result of a data breach; and satisfy the full array of damages sought by such third parties, including damages for future injuries resulting from the anticipated improper use of data. These considerations are increasingly important because the policies available in today’s market are not standardized. While many absorb some of the costs associated with notification and fraud monitoring, existing forms may not protect against damages sought for susceptibility to identity theft.
The Remijas decision
Last fall, the Seventh Circuit reviewed the “substantial risk” standard for Article III class action standing in Remijas v. Neiman Marcus Group and held that even a 2.5 percentage of compromised credit card holders is enough to show a substantial risk to an entire universe of credit card holders with breached data. 794 F.3d 688, 693 (7th Cir. 2015).
Read more